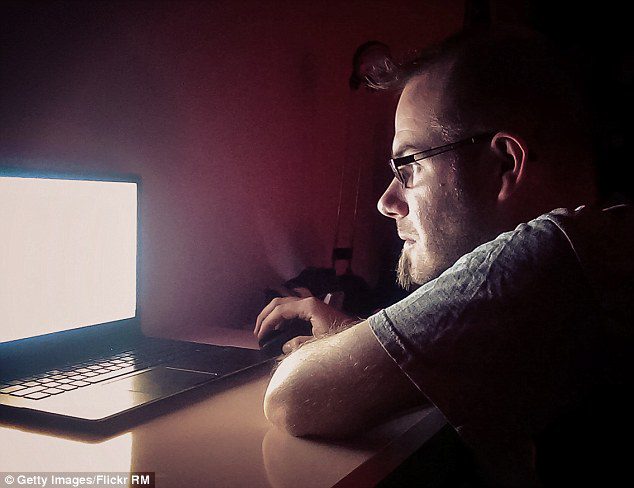
In my Cyber Safety parent workshop, I ask parents where is the safest place for their child to be? After asking thousands of parents this question, I always hear the same answer: In their home. What is the fear of allowing their child unsupervised outside the home? The general concern among parents is the possibility of their child meeting someone they don’t know, someone dangerous. Although this possibility does exist, the rate of violent crime across the country has dropped significantly in the last twenty years. The chance that a teen will ever come in physical contact with a sexual predator in their neighborhood is very low; let alone being snatched off the street—an occurrence that is extremely rare. When we look again at the picture of a child sitting alone, safely in his room, we see something new. The fear of their child meeting someone they don’t know is missed placed. The child sitting on their bed now has a mobile device in their hands with Internet and social media access. Our social media connected teen is now not only exposed to the people in their neighborhood, or just the people in the United States. She is now sharing intimate details about herself to potentially 2.5 billion people on the Internet. This translates to millions of sexual predators who have access to your child in your own home.
In December of 2014, the Cleveland Police department reported an all too common story of a ten-year-old girl who was groomed by sexual predators through her iPad.
The girl was given the tablet to help with her schoolwork, but unfortunately, the mobile device was used for social media applications like Snapchat and Skype. After about a month of unmonitored use, her mother checked the device and was horrified to discover that her daughter had been targeted by at least 16 men.
The ten-year-old ...
Choose a Family Premium Membership for continuous access to exclusive resources, monthly online risk updates, practical safety tools, and a free 30-minute counseling session, along with guides, videos, webinars, app reviews and curated content.
Free for first 7 days
Free for first 7 days
Free for first 7 days
Free for first 7 days
Free for first 7 days
Free for first 7 days