Yik Yak – What Parents Need to Know
Parents need to be on the look out for Yik Yak on their children’s smart phones. This new social media app that launched just three months ago is spreading like […]
Clayton Cranford is a retired Sergeant from Orange County Sheriff's Department in California and owner of Total Safety Solutions LLC. Clayton is one of the nation’s leading law enforcement educators on social media, child safety, and behavioral threat assessments. Clayton is the author of the definitive book on cyber safety for families, “Parenting in the Digital World.” Clayton has more than 20 years of teaching experience and was awarded the 2015 National Bullying Prevention Award from the School Safety Advocacy Council, and the 2015 American Legion Medal of Merit. Clayton was a member of the County's Behavioral Threat Assessment Team, Crisis Negotiation Team, School Resource Officer program, and Juvenile Bureau.
Parents need to be on the look out for Yik Yak on their children’s smart phones. This new social media app that launched just three months ago is spreading like […]

Pheed is best described as a hybrid of Facebook, Instagram, Twitter and YouTube — except that you can require others to pay a premium to access your personal channel. Why […]

Block adult web content in iOS7 on iPods, iPads and iPhones As you may know Apple does offer some level of parental control for iPods, iPhones and iPads through Restriction […]
Tumblr is like a cross between a blog and Twitter: It’s a streaming scrapbook of text, photos and/or videos and audio clips. Users create and follow short blogs, or “tumblelogs,” […]
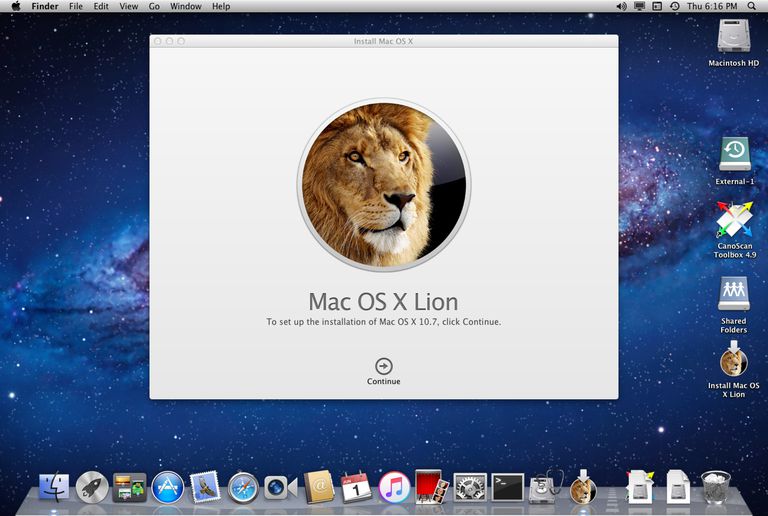
How to Set Parental Controls on Mac OS X It isn’t hard to look around and see the social and technological influence that Apple has had on our society. They’ve […]

I tell parents cyber safety is a moving target. The app popular with teens today is often out of vogue in just a few months. Today, Instagram is on every […]

Criminologist and cyberbullying expert Justin Pachin says zero tolerance policies often don’t work. He cites the recent case in the U.S. of a boy who bit into a Pop-Tart in […]

Vine is rapidly becoming a popular app for teens to share 6 second looped videos. 1. Vine is free, and it’s easy to sign up.Unlike paid apps where you get a […]

If you search the web, you’ll discover that Tinder is all about hooking up and still the age restriction to use the app is only 12. This dating app […]

There is no one single method in which online predators work. But there are several methods that can have been identified as how online predators locate their victims and get […]